Ukraine initially seemed to be the target of the cyberattack, which started on June 27, affecting Ukrainian government computer networks, websites of banks, major industrial enterprises, the postal service, Kyiv’s international airport, and the Chernobyl nuclear power plant. But the attack also hit other countries and international companies around the world.
The virus’s pace appeared to slow by June 28, partly because the malware seemed to require direct contact between computer networks, a factor that may have limited its spread in regions with fewer connections to Ukraine.
However, businesses in the Asia-Pacific region reported some disruptions on June 28 with the operations of several European companies hit.
Mysterious Shadowbrokers
Like last month’s outbreak of ransomware, dubbed WannaCry, the new attack spread by using an intrusion tool that cybersecurity experts believe was created by the U.S. National Security Agency (NSA) and released online by a still-mysterious group known as the Shadowbrokers.
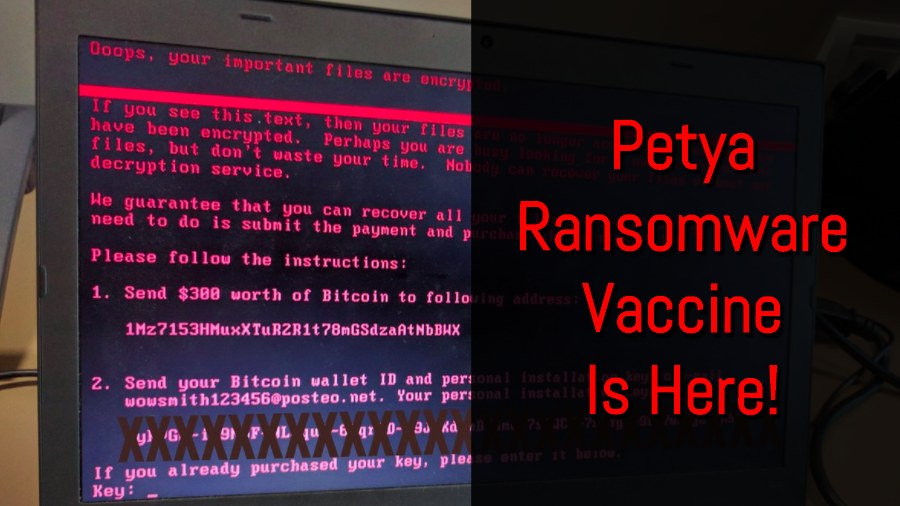
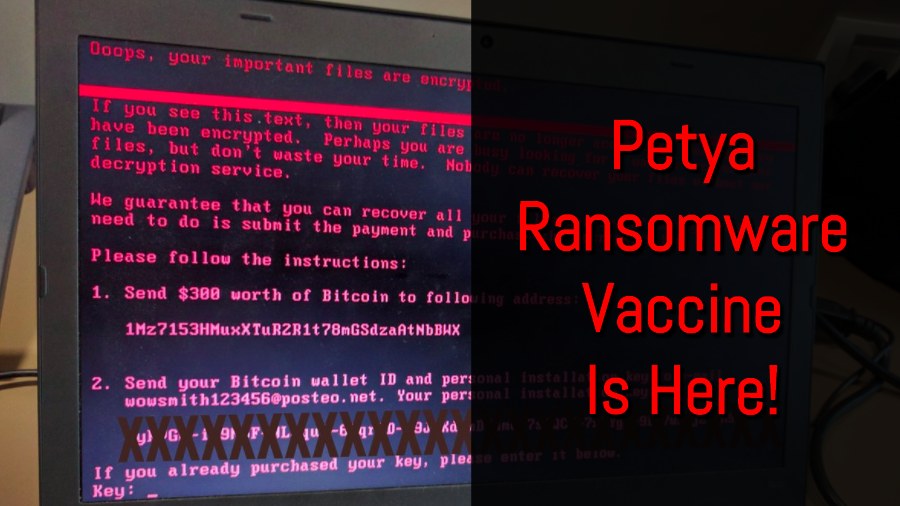
The malicious software freezes the user’s computer until an untraceable ransom is paid in the digital Bitcoin currency.
Russian antivirus firm Kaspersky Lab said it had traced some 2,000 attacks — most of them in Ukraine, Russia, and Poland.
Ukrainian Prime Minister Volodymyr Hroysman said on June 27 that his country was suffering an “unprecedented” cyberattack but that “vital systems” were not being affected.
Deputy Prime Minister Pavlo Rozenko said the government’s computer network went down and the central bank experienced disruption to operations as did banks and firms, including the state power distributor.
Other Countries Hit
Russia’s Central Bank said there were isolated cases of lenders’ IT systems being infected. One consumer lender, Home Credit, had to suspend client operations.
Rosneft, Russia’s largest oil company and one of the world’s biggest crude producers by volume, said its servers were attacked but that oil production was not affected because it switched over to backup systems.
Elsewhere, British advertising firm WPP, U.S. law company DLA Piper, and Danish shipping giant A.P. Moller-Maersk were also infected.
The White House National Security Council said government agencies were investigating the attack and that the United States was “determined to hold those responsible accountable.”
The U.S. Department of Homeland Security advised those targeted by the attacks not to pay the ransom, saying there was no guarantee that access to files would be restored. It said it was monitoring the attacks and coordinating with other countries.
No ‘Kill Switch’
Security experts believe the impact of the current attack will be smaller than WannaCry, which hit hundreds of thousands of computers worldwide after it emerged on May 12.
The experts say many computers have been patched with Windows updates in the wake of last month’s WannaCry attack to protect them against attacks using the same exploit, known as “Eternal Blue.”
Nonetheless, the attack could be more dangerous than traditional strains of ransomware because it makes computers unresponsive and unable to reboot, they say.
Meanwhile, the BBC reported on June 28 that security researchers have discovered a “vaccine” for the cyberattack — a single file that can stop the attack from infecting a machine.
However, it said, experts could not find a so-called kill switch that would block the ransomware from spreading to other vulnerable computers.